Does my business need secure destruction of IT assets?
Businesses of all shapes and sizes are increasingly reliant on technology to function effectively in our modern world. Whether you are a mom and pop shop or a multi-national corporation, you need to seriously consider how you manage retired computers and devices along with the information they carry. So, does you business need to securely destroy IT assets? Let’s begin to explore this question by first defining what constitutes an IT asset.
What is an IT Asset?
The simplest definition of an IT asset is any data bearing media or hard drive. This can include smartphones, tablets, disks, external drives, LTO tapes, and more. Essentially, anything that stores digital information. Keep in mind that many office electronics now store data. For instance, many copiers, scanners, and printers have hard drives. This means that it is possible for every image you have ever copied, printed, or scanned to be saved.
What types of data should be protected?
Not all data is created equal. An email about where to eat lunch and a report on company finances are not of equal value. So, what information should you focus on protecting? While specific regulations vary based on your location and industry, in broad terms, most legal and ethical requirements center on protecting the personally identifying information of both employees and consumers. Again, the definition of personally identifying information can vary across jurisdictions, but here are some widely accepted examples:
- Full names
- Birth dates
- Phone numbers
- Addresses
- Employment related information
- Employer ID number
- Passport information
- Medical information
- Bank information
- Credit card information
- Electronic or digital accounts
- Passwords
- School ID numbers
This list is not comprehensive. But it should give you an idea of the types of information you need to safeguard to protect your consumers and your employees both past and present. In addition to these legal and ethical obligations, businesses should also prioritize the protection of business critical information. This refers to information that is necessary for the functioning of your business. Also, data that if exposed to competitors or criminals could potentially harm your business. Examples of business critical information include:
- Finance reports
- Intellectual property
- Trade secrets
Business devices that should be securely destroyed
Your business may have a vast IT department or just a single computer or tablet. Regardless of size, protecting data is still a critical activity. So, here are some of the devices and media you should mark for secure destruction after they are retired from use:
- Computer hard drives
- Laptops
- Tablets
- Smartphones
- External drives
- LTO tapes
- Disks
- Hard drives from printers, scanners, copiers, etc.
- Any device which potentially contains data
At this point, you may wonder why destruction of these devices is important. Many people still believe that deleting data or doing a factory reset on a device will erase the data. However, this is NOT true. Deleting and factory resets simply make room for new data to be written. They do NOT erase data. Recovering the data can be as simple as connecting the device to a computer and browsing the files, or using a readily available data recovery software program.
Using a wiping program is another misleading option for the disposal of IT assets. Wiping programs generate code to overwrite the existing data. In theory, this would allow a device to be resold because the data is destroyed. However, wiping programs can leave data behind. Residual data poses a major threat if the asset continues to circulate. While wiping sounds like an attractive option, it cannot guarantee the data is destroyed. Therefore, we always recommend the physical destruction of IT assets.
How to destroy IT assets
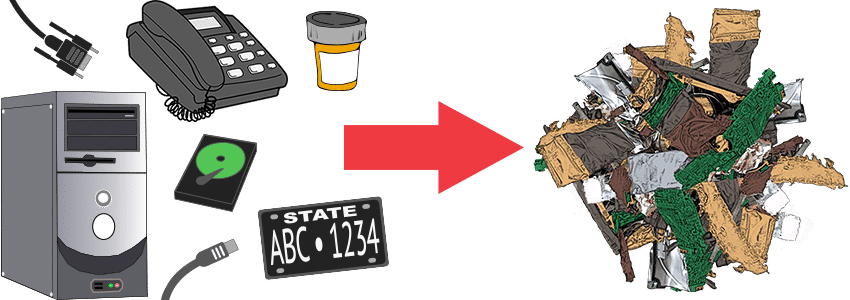
You have IT assets and need to protect the data they hold. How do you securely dispose of them? First, research destruction companies in your area. You may find this service listed as hard drive destruction, media destruction, or IT asset disposition. If possible, find a service provider that will pick up from your location. Avoid the cost and potential problems of shipping items to a long-distance facility.
Second, find out how the service provider will destroy your items. Some destruction companies wipe devices and then resell them. This is not ideal. Guarantee your devices will be physically destroyed by either degaussing (with magnets) or crushing and shredding. These are the only sure ways to make the data completely unreadable.
Third, use a service provider with an e-waste and electronics disposal program. These providers work to recycle materials after the devices have been destroyed. This is a win-win. You protect your information and responsibly recycle.
For more information on the disposal of IT assets check out our Hard Drive / Media Destruction services and E-Waste program.
